Logpoint, now Guardsix, positions itself as a converged SIEM platform that combines SIEM, UEBA, SOAR, and case management, and it supports both SaaS and on-premise deployment. Its pricing story is also different from many legacy SIEM tools because the company emphasizes predictable pricing that is not driven purely by log volume.
In this review, we look at how Logpoint pricing works, what actually drives cost, where the product is strong, where buyers should be careful, and which alternatives are worth considering. The goal is simple: help buyers understand whether Logpoint is a good fit, not just whether it looks good in a demo.
Disclaimer: Logpoint now operates under the Guardsix brand. This review uses “Logpoint” where relevant to match search intent, but current company, product, and pricing information may appear under the Guardsix name.
What is Logpoint, now Guardsix?
Logpoint, now Guardsix, is a SIEM and security operations platform designed for threat detection, investigation, response, and compliance. It collects and analyzes data across endpoints, networks, cloud services, and business applications, includes more than 1,000 pre-built detection rules aligned to MITRE ATT&CK, and provides pre-configured dashboards for frameworks such as GDPR, HIPAA, and PCI DSS. Logpoint also states that the platform can be deployed on-premise for data sovereignty or in the cloud through Logpoint SaaS.
In simple terms, Logpoint is a SIEM-first security operations platform. It is designed for teams that need centralized log collection, threat detection, investigation workflows, compliance reporting, and automated response support. It is not primarily an engineering observability platform. That distinction matters because some buyers searching for “Logpoint pricing” are really comparing SIEM tools, while others may actually need something broader than SIEM.
Logpoint pricing packages
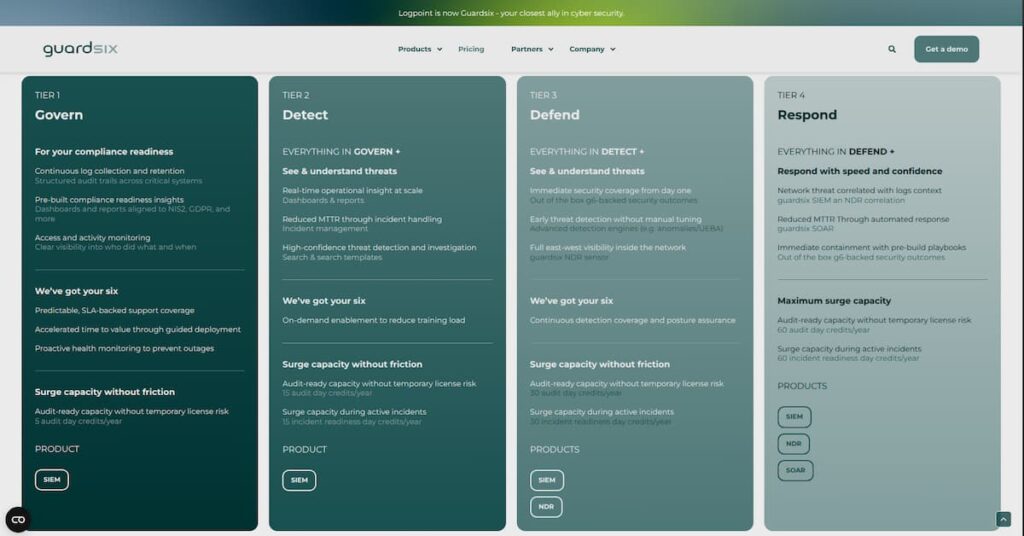
Logpoint now operates under the Guardsix brand, and the current Guardsix pricing page presents four pricing packages: Govern, Detect, Defend, and Respond. These packages are structured as a progression, with each tier adding more capabilities on top of the previous one. Guardsix also says its pricing model is flat and transparent, and that pricing depends on the number of nodes, devices, or entities in the environment, the products and capabilities selected, and the preferred level of services and support.
Disclaimer: Logpoint now operates under the Guardsix brand. The package details below reflect the current Guardsix pricing page at the time of writing. Final pricing still depends on deployment model, product mix, support tier, and commercial agreement.
| Tier | Package | Focus | What it includes |
|---|---|---|---|
| Tier 1 | Govern | Compliance readiness | Log collection, audit trails, compliance dashboards, access and activity monitoring |
| Tier 2 | Detect | Threat visibility and investigation | Everything in Govern, plus dashboards, incident management, and search templates |
| Tier 3 | Defend | Early detection and network visibility | Everything in Detect, plus NDR, UEBA, and advanced detection |
| Tier 4 | Respond | Faster response and containment | Everything in Defend, plus SOAR, SIEM-NDR correlation, and response playbooks |
This package structure is important because it changes how buyers should think about Logpoint pricing. The platform is not presented only as a single SIEM license. Instead, the current pricing page frames it as a tiered security-operations offering where compliance, detection, network visibility, and response capabilities expand as buyers move from Govern to Respond.
Logpoint pricing comparison
Buyers looking at Logpoint usually want to understand not only whether it is affordable but also how its pricing logic differs from other tools. The clearest differentiator in Logpoint’s own language is that it tries to shift pricing away from pure log-volume volatility and toward a more stable environment-based model.
| Platform | Pricing visibility | Core pricing logic | Deployment options | Best fit |
| Logpoint | Limited public pricing; quote-led | Nodes, devices, entities, data sources; SIEM SaaS includes ingestion and storage | SaaS and On-premise | Security teams that want more predictable SIEM economics |
| Typical cloud-native SIEMs | Often clearer on usage billing | More directly tied to data ingestion, storage, retention, or cloud consumption | Usually cloud-first | Teams already standardized on a cloud vendor |
| Self-managed SIEM stacks | No vendor list price in the usual sense | Software may be open or licensed separately | Self-hosted | Teams with strong in-house platform capability |
| Observability platforms such as CubeAPM | Usually clearer on telemetry-based pricing | More focused on logs, metrics, traces, and infrastructure | Customer cloud or on-premise | Engineering-led teams whose real need is broader telemetry control |
How Logpoint pricing works
The official SIEM pricing calculator is the best source here. Logpoint says its total cost of ownership model is transparent, predictable, and independent from the volume of logs. It also says that server licensing is based on data sources and workstations and that pricing depends on the environment and support needs. On the same page, the company says its pricing model is flat and based on the organization’s number of nodes, devices, and entities.
Disclaimer: The table below summarizes Logpoint’s publicly described licensing structure, not a full public rate card. Exact pricing depends on the products selected, deployment type, support requirements, and contract terms.
| Product area | Licensing model based on | Publicly shown minimum / note |
| SIEM Server | Nodes | Minimum licensing count of 100 nodes |
| SIEM SaaS | Data ingestion and storage | 20 GB ingestion and 90 days retention shown on the pricing page |
| NDR | Devices | Standard/Pro and Enterprise tiers shown |
| Automation | Entities | Requires SIEM Server or SIEM SaaS |
| Case Management | Entities | Requires Automation license |
What actually drives Logpoint cost
The biggest cost drivers are clear from the official pricing page.
- Number of nodes
- Number of devices
- Number of entities
- Number and type of data sources
- Support and service tier
- Deployment model, such as SaaS or on-premise
- Expansion into adjacent capabilities like Automation and Case Management
A better way to think about Logpoint pricing is not “What is the monthly price?” but “What exactly am I licensing?” A small SIEM Server deployment, a SaaS deployment, and a broader rollout with Automation and Case Management can look very different commercially even before support and implementation scope are added.
How Logpoint works: Architecture and deployment
SaaS deployment
Logpoint’s SaaS documentation says customers are given access through the Logpoint Portal and that several system settings are pre-configured in the SaaS environment. This is the lighter operational path and is the more natural fit for teams that want faster deployment and less platform-management burden.
On-premise deployment
The official SIEM documentation explicitly says Logpoint can be deployed on-premise for complete data sovereignty. That is important for regulated industries, public sector buyers, and organizations with strict internal policies on where security telemetry can live.
Why this matters commercially
Deployment model is not just a technical choice. It changes operational responsibility, infrastructure burden, internal staffing needs, and how the buyer should think about total cost. SaaS reduces operational overhead. On-premise may be the right fit for compliance or data-control reasons, but it usually adds internal cost that sits outside the software license itself. That is the same decision logic your sample uses in its deployment sections, and it is very relevant for Logpoint as well.
What is included in Logpoint?
Logpoint’s official SIEM documentation presents the platform as more than a basic log collector. The public docs clearly position it as a broader security operations product.
Core platform capabilities
| Capability | What the official docs say |
| SIEM | Threat detection, investigation, and response in one solution |
| Detection content | Over 1,000 pre-built detection rules aligned to MITRE ATT&CK |
| Compliance support | Pre-configured dashboards for GDPR, HIPAA, PCI DSS, and others |
| SOAR support | Integrated SOAR capabilities for automated response |
| Deployment flexibility | Available on-premise or through Logpoint SaaS |
This matters because value in a SIEM purchase is not only about ingestion. It is about how much of the SOC workflow the product can support without forcing the team into too many extra tools.
Real-world cost scenarios
Scenario 1: Small security team with straightforward SIEM needs
Situation: A small internal security team wants centralized event monitoring, basic detection coverage, and compliance-oriented visibility without a pricing model that jumps every time log volume spikes during an incident.
Why Logpoint can fit:
- Predictable pricing is attractive when budgets are tight
- Built-in detection content reduces early setup effort
- The platform is clearly SIEM-first, which can be simpler than adapting a broader data platform
- SaaS offers a lighter operational path for teams without deep platform capacity
Main cost levers:
Disclaimer: The scenarios below are illustrative, not official pricing quotes. Actual Logpoint costs vary based on deployment model, product mix, support tier, and commercial agreement.
| Cost factor | Likely impact |
| Number of nodes | Moderate |
| Number of data sources | Moderate |
| Support needs | Low to moderate |
| Deployment choice | Moderate |
What this shows: Logpoint can make sense for smaller teams when the key goal is predictable SIEM value, not extreme self-serve simplicity.
Scenario 2: Mid-market team expanding security operations
Situation: The organization now has more systems, more identities, more data sources, and more pressure to improve investigations and response workflows.
Why Logpoint becomes more attractive:
- Cost predictability matters more as the monitored estate grows
- Broader platform components like Automation and Case Management become more relevant
- Support and service tiers matter more in production use
- The value of one security platform grows when analyst workflow gets more complex
Main cost levers:
Disclaimer: The scenarios below are illustrative, not official pricing quotes. Actual Logpoint costs vary based on deployment model, product mix, support tier, and commercial agreement.
| Cost factor | Likely impact |
| Number of nodes | Major |
| Number of devices and entities | Major |
| Data-source footprint | Major |
| Support tier | Moderate to major |
| Deployment model | Major |
What this shows: The bigger and more mature the environment becomes, the more Logpoint’s predictability story matters.
Scenario 3: Regulated enterprise needing stronger data control
Situation: A regulated enterprise needs SIEM, compliance reporting, and stricter control over telemetry location and platform operations.
Why Logpoint is often relevant here:
- On-premise deployment is officially supported
- Compliance dashboards are part of the documented product story
- Predictable pricing can be easier to justify than pure ingestion-led commercial models
- Enterprise support and service scope become part of the value discussion
Main cost levers:
Disclaimer: The scenarios below are illustrative, not official pricing quotes. Actual Logpoint costs vary based on deployment model, product mix, support tier, and commercial agreement.
| Cost factor | Likely impact |
| On-premise deployment | Major |
| Support and services | Major |
| Number of entities and devices | Major |
| Compliance and reporting requirements | Major |
What this shows: Logpoint’s strongest strategic fit is often in security-led organizations with real governance, sovereignty, or compliance needs.
Hidden costs buyers should plan for
Even with pre-built detection content, SIEM rollouts still require connector onboarding, normalization checks, rule tuning, alert validation, and reporting setup. That effort is part of the true cost, even if it does not appear as a neat line item on a pricing page. This is a practical inference from the product’s scope and deployment model.
Because Logpoint’s pricing and product positioning explicitly reference data sources, buyers should expect onboarding effort around source configuration, parser validation, and ongoing coverage quality.
Logpoint says it offers several services and support levels to help customers on their maturity journey. Buyers should clarify what support is included, what requires a higher tier, and how incident escalation works.
On-premise deployment can be the right choice for sovereignty or policy reasons, but it also brings infrastructure, maintenance, resilience, upgrades, and staffing overhead. That operational cost needs to be compared with SaaS, not ignored.
What users seem to like
The current public review footprint is not huge, but GetApp does provide a useful directional snapshot. It shows LogPoint at 4.9 out of 5 based on 11 verified reviews, with strong visible scores for ease of use and a high likelihood-to-recommend score.
Across the official product story and the review evidence available, the most likely strengths are:
- Easier budgeting than tools whose cost grows directly with ingestion
- Strong fit for SIEM-first use cases
- Good deployment flexibility
- Solid ease-of-use perception in the small current GetApp review sample
Where buyers should be careful
A neutral review also needs to cover limits.
First, Logpoint still has limited public price transparency. Buyers can understand the pricing logic, but they still need a quote for precise budgeting.
Second, the platform’s licensing story is more layered than a simple “node-based SIEM” label suggests. SIEM Server, SIEM SaaS, Automation, and Case Management do not all use the same commercial unit. That is manageable, but buyers should not assume the same metric applies to everything.
Third, some review content in your uploaded sources points to limits around interface polish, handling certain log formats, and support consistency in some environments. For example, one uploaded review mentions challenges with multiple log types, occasional discarded logs, and uneven L1 support, while another review summary surfaced in Gartner Peer Insights highlights issues with indexing, tables, and larger searches. These are not universal verdicts, but they are meaningful enough to test during evaluation.
Review snapshot
| Review source | Visible rating | Review count | Takeaway |
| GetApp | 4.9 / 5 | 11 | Positive but small sample |
| Uploaded third-party review content | Mixed qualitative feedback | Various | Pricing and ease can look good, but log handling and support need validation |
The safest reading is that Logpoint is generally well regarded by a small current public review pool, but serious buyers should rely more on proof-of-concept testing and direct reference calls than on star ratings alone.
When Logpoint is a good fit
- Security teams that want a SIEM-first platform
- Organizations that care about predictable pricing more than self-serve simplicity
- Regulated environments that need on-premise or sovereignty-friendly deployment
- SOC teams that want detection, investigation, compliance, and response support in one product
When Logpoint may not be the best fit
- Teams that want a fully public list price
- Organizations looking mainly for engineering observability rather than security operations
- Buyers who only need lightweight log management
- Teams that want the simplest possible commercial model across every module and add-on
Alternatives worth considering
CubeAPM
CubeAPM is the strongest adjacent alternative here for teams whose real need is broader observability rather than a pure SIEM workflow. Its official site positions it as a full-stack observability platform covering APM, log management, infrastructure monitoring, Kubernetes monitoring, real user monitoring, and synthetic monitoring, with deployment inside the customer’s cloud and pricing from $0.15 per GB on its pricing page. That makes it more relevant for engineering-led teams that want unified telemetry visibility and stronger data control than for buyers looking for a classic SOC platform.
New Relic
New Relic is a strong alternative for teams that want mature full-stack observability rather than a SIEM-first product. New Relic’s official positioning centers on observability across applications and infrastructure, which makes it more suitable for software performance, reliability, and troubleshooting use cases than for a traditional security operations workflow. This is usually the better fit when the core problem is application and platform visibility rather than threat detection and case-driven SOC operations.
SigNoz
SigNoz is a strong open-source alternative for teams that want OpenTelemetry-native observability with flexible deployment. Its official site describes it as an open-source observability platform for traces, metrics, and logs, with support for self-hosting or cloud deployment. That makes it appealing for teams that want broader observability, open standards, and lower entry cost, but it is not a like-for-like SIEM replacement for Logpoint.
Microsoft Sentinel
Microsoft Sentinel is the most direct SIEM alternative in this group. Microsoft describes it as a cloud-native SIEM with capabilities for threat detection, investigation, response, and hunting across multicloud and multiplatform environments. It is usually the strongest fit for organizations already invested in the Microsoft ecosystem, while Logpoint may be more appealing to buyers that want on-premise deployment flexibility and a different pricing approach.
Comparison table
| Tool | Best for | Key strengths | Main trade-off |
| CubeAPM | Teams that need broader observability beyond SIEM | Full-stack observability across logs, metrics, traces, infrastructure, and Kubernetes; | Not suited for teams seeking off-prem solution |
| New Relic | Engineering teams focused on application and infrastructure observability | Mature full-stack observability | Less suited to buyers looking for a SIEM-first SOC workflow |
| SigNoz | Teams that want an OpenTelemetry-native open-source observability option | Open-source, traces-metrics-logs in one platform, self-hosted or cloud deployment | Not a direct SIEM replacement |
| Microsoft Sentinel | Microsoft-centric organizations that want cloud-native SIEM | Direct SIEM use case with threat detection, investigation, response, and hunting | Best fit is often tied to Azure and Microsoft security stack alignment |
The right alternatives depend on what the buyer is actually trying to solve.
If you are still comparing options, it helps to review tools by actual use case, pricing model, deployment fit, and operational overhead. Buyers who are not fully sure whether they need a SIEM-first platform or broader observability should also compare adjacent tools before making a final decision.
You can also review:
Conclusion
Logpoint is a serious SIEM option for organizations that care about predictable security operations pricing, deployment flexibility, and a broader security workflow than basic log management alone. Its biggest commercial strength is not a flashy public pricing page. It is the way the company frames cost around the shape of the environment and the security outcome, rather than only around data spikes. That makes it especially relevant for security-led teams and regulated organizations. The tradeoff is that exact pricing still requires a quote, and buyers need to understand that different product areas use different licensing units. For teams buying a SIEM, Logpoint deserves a real look. For teams whose actual need is broader observability and telemetry control, an adjacent platform like CubeAPM may be worth evaluating alongside the SIEM shortlist.
FAQ
1. How much does Logpoint cost in 2026?
Logpoint does not publish a full public rate card. It uses a pricing calculator and quote-led process and says pricing depends on the environment and support needs.
2. Is Logpoint pricing based on log volume?
Not in the simple way many SIEM tools are. Logpoint says its model is independent from log volume, but the pricing page also shows that different parts of the platform use different licensing units, including nodes, ingestion and storage, devices, and entities.
3. Is Logpoint available as SaaS and on-premise?
Yes. The official documentation says Logpoint is available both on-premise and through Logpoint SaaS.
4. Does Logpoint include SOAR capabilities?
Yes. The official SIEM documentation says the platform includes integrated SOAR capabilities for automated response.
5. Is Logpoint a good fit for regulated industries?
It can be, especially because the platform supports on-premise deployment and includes compliance-oriented dashboards for frameworks such as GDPR, HIPAA, and PCI DSS.
6. What do reviews say about Logpoint?
GetApp currently shows LogPoint at 4.9 out of 5 based on 11 reviews, which is positive but still a small sample. Some additional uploaded review content also suggests buyers should validate log handling, performance, and support quality during evaluation.
7. Is CubeAPM a direct alternative to Logpoint?
Usually not. CubeAPM is more relevant when the buying question shifts from SIEM to broader observability, infrastructure visibility, and telemetry control.







