Platform selection has moved well beyond feature checklists. Engineering teams evaluating observability in 2026 are asking harder questions: Who owns the telemetry data? What happens to the bill when traffic spikes or team size doubles? Does the platform scale with OpenTelemetry natively? Can logs, traces, and metrics be investigated together without switching tools?
This guide compares three distinct platforms, Graylog vs. Grafana vs. CubeAPM, across architecture philosophy, MELT signal coverage, pricing behavior, sampling strategies, data retention, and real-world operational fit. The goal is to give engineering teams and platform architects an honest, vendor-neutral basis for evaluation rather than a marketing comparison.
Quick Comparison: Graylog vs Grafana vs CubeAPM
| Dimension | CubeAPM | Graylog | Grafana Cloud |
| Primary Focus | Full-stack observability | Log management and SIEM | Dashboards and composable observability |
| Deployment | Vendor-managed self-hosted | Self-hosted, hybrid, or cloud | Self-hosted LGTM or managed cloud |
| Pricing Model | $0.15/GB, no user fees | From $15K/year | Usage-based by signal |
| MELT Coverage | Full MELT | Logs-first | Full MELT with LGTM |
| OpenTelemetry | OTel-native | OTel log ingest | Strong OTel support |
| Data Ownership | Customer environment | Customer or Graylog Cloud | Self-hosted or Grafana Cloud |
| Retention | Long-term/unlimited by plan | Configurable; 30–40 day default index window | 30 days logs/traces; 13 months metrics on Pro |
| Sampling | Smart trace sampling | Log filtering/routing | Adaptive Traces tail sampling |
| Best For | Full-stack OTel observability | Log/SIEM-heavy teams | Flexible dashboards and integrations |
How We Evaluated These Platforms
To keep this comparison grounded and reproducible, the platforms were evaluated against a consistent set of technical and commercial assumptions.
Test Architecture Assumptions
- Kubernetes-based microservices architecture
- JVM and Node.js services with distributed tracing enabled
- Centralized log ingestion from multiple sources
- 30, 125, and 250 engineer team models
Telemetry Assumptions
- Logs: 250 to 1,500 GB/month (scaled by team size)
- Traces: 20 to 200M spans/month
- Metrics: Standard infrastructure and application metrics
- Retention: 30 to 90 days baseline for cost modeling
This comparison focuses on architectural design and pricing behavior at scale. It does not evaluate entry-level free-tier experiences in isolation, since most of the meaningful cost and coverage differences emerge under real production workloads.
Architecture Philosophy
Deployment Model and Data Control
The biggest difference between these platforms is not only feature coverage. It is where telemetry data lives and who controls the operating environment.
| Dimension | CubeAPM | Graylog | Grafana Cloud |
| Deployment | Vendor-managed self-hosted | Self-hosted, hybrid, or cloud | Self-hosted LGTM, Grafana Cloud, or BYOC |
| Data location | Customer cloud or on-prem | Customer infra or Graylog Cloud | Self-hosted, Grafana Cloud, or customer AWS/GCP via BYOC |
| Operational ownership | CubeAPM manages ops; customer owns data | Customer manages self-hosted; Graylog manages cloud | Customer manages self-hosted; Grafana manages Cloud/BYOC |
| Self-hosted option | Yes | Yes | Yes, via OSS LGTM stack |
| Compliance fit | Strong for data-control needs | Strong when self-hosted | Strong when self-hosted or using Federal Cloud |
For regulated teams, deployment model matters as much as features. CubeAPM keeps telemetry inside the customer’s own environment. Graylog supports on-prem, hybrid, and cloud deployment. Grafana can be self-hosted through the LGTM stack, used as Grafana Cloud, or deployed through BYOC in a customer AWS or GCP account. Grafana Federal Cloud is also FedRAMP High Authorized and DoD IL5 compliant.
Feature Evaluation
Core Focus
CubeAPM is built for teams that want full-stack observability without giving up control over telemetry data. It brings metrics, events, logs, and traces together in an OpenTelemetry-native platform that runs inside the customer’s cloud or on-prem environment. This makes it a strong fit for teams that need unified visibility, predictable ingest-based pricing, and data ownership.

Graylog is built mainly for centralized log management and SIEM. Its strength is collecting, processing, searching, and analyzing large volumes of log data for operations, security, and compliance workflows. It fits teams whose main priority is log investigation rather than native tracing-first APM.
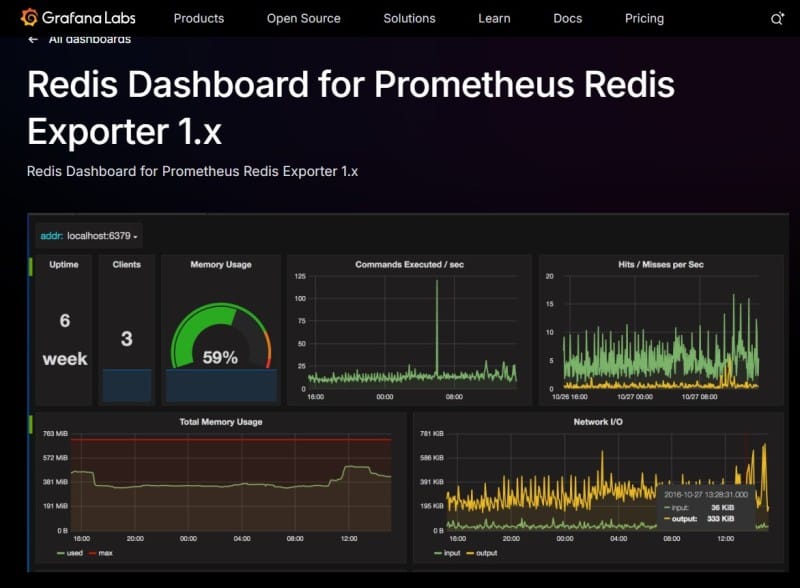
Grafana is built for flexible observability and visualization. Its strength is a composable ecosystem built around Loki for logs, Tempo for traces, Mimir or Prometheus for metrics, and Grafana dashboards. It works best for teams with enough SRE capacity to assemble and operate a multi-signal stack.
MELT Coverage
CubeAPM provides full MELT coverage across metrics, events, logs, and traces, with correlation built into the same platform. Its strength is not just collecting all four signals but also letting teams investigate them together inside their own environment without sending data to an external SaaS backend.
Graylog is strongest on the log side of observability. It gives teams powerful log ingestion, search, enrichment, alerting, and security analysis. However, it is not a full native MELT platform in the same way as CubeAPM or Grafana because distributed tracing and full cross-signal observability are not its main design center.
Grafana delivers full MELT coverage when all components of the LGTM stack are in place. Loki handles logs, Tempo handles traces, Mimir or Prometheus handles metrics, and Grafana dashboards provide visualization across all signals. Application Observability in Grafana Cloud ties them together with service-level views and RED metrics.
Sampling Strategy
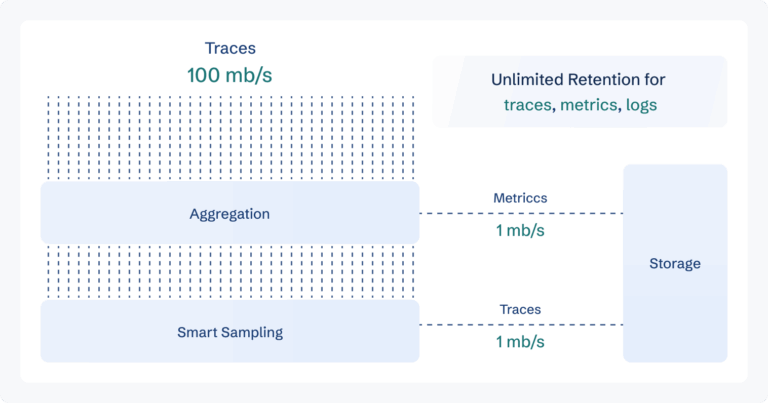
CubeAPM implements context-aware smart sampling natively. The platform automatically prioritizes the retention of anomalous traces, high-latency spans, and error-path traces, while applying more aggressive sampling to healthy request flows. This means the data that matters most for debugging is disproportionately retained, while routine baseline traffic is sampled at a higher ratio.
Graylog uses rule-based filtering and routing at the pipeline level. Teams configure pipeline rules to route logs to active indexed storage, warm storage tiers, or a data lake based on source, severity, or content. This is not trace-aware sampling but log-level routing, which is useful for controlling log ingestion costs but does not apply to distributed tracing workloads.
Grafana introduced Adaptive Traces as a generally available feature in October 2025. Adaptive Traces provides managed tail sampling inside Grafana Cloud, where the sampling decision is deferred until a complete trace is collected. Teams define policies to retain traces with errors, high latency, or other critical attributes, while dropping routine traces. Grafana reports customers typically reduce ingested trace volumes by 75 to 90% with Adaptive Traces. For self-hosted Grafana deployments, tail-based sampling can be configured in Grafana Alloy or the OpenTelemetry Collector but requires the team to operate the sampling infrastructure.
Real-World Debugging Scenario: Intermittent API Latency Spike
A payments service is intermittently spiking from 80ms to 1.9 seconds during peak hours. An alert fires, and the on-call engineer begins an investigation.
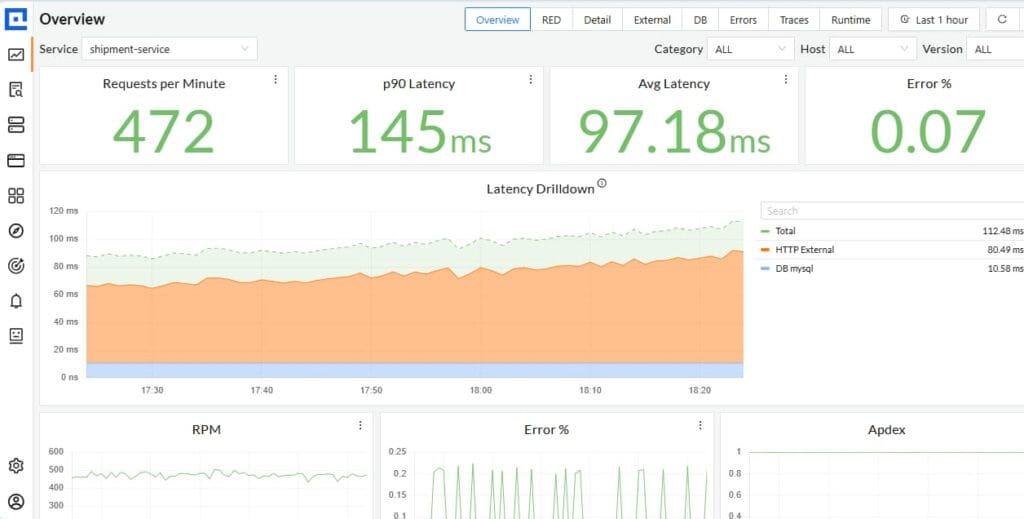
Using CubeAPM
Smart sampling retained the high-latency traces in full fidelity while healthy baseline traffic was sampled at a higher ratio. The trace view shows the exact database span (an ORM query against the orders table, 1.74 seconds) with full span attributes. The engineer pivots directly from the trace to correlated infrastructure metrics showing CPU throttling on the database pod and correlated application logs showing connection pool exhaustion warnings, all within the same platform. No data crossed an external boundary. Historical trace and log data beyond 30 days is available for trend analysis without additional retention charges.
Using Graylog
The investigation begins in the log search interface. The engineer filters structured logs by service name and time window, looking for error patterns or unusual field values correlated with the spike. Graylog’s pipeline processor has already parsed and enriched relevant fields for filtering. The team can identify error messages and log-level patterns, but trace-level span data showing the specific downstream call that introduced the latency is not available natively. A separate APM tool would be required to identify the slow span. Investigation time increases because context must be rebuilt across tools.
Using Grafana
With Application Observability in Grafana Cloud, the service map highlights the payments service and shows downstream dependency health. The engineer drills into Tempo and finds a slow database span averaging 1.8 seconds during the spike window. Loki is used to pull correlated log lines for the affected time range and service. Infrastructure Monitoring shows the database pod’s CPU was saturated at 92 percent during the incident window. With Adaptive Traces running, the high-latency traces were retained in full, while the routine request volume was sampled aggressively. The investigation covers traces, logs, and infrastructure metrics within Grafana Cloud, though the full experience depends on the LGTM stack being correctly assembled and connected.
All three platforms can lead to a resolution, but the investigation workflow, signal availability, data ownership model, and stack complexity differ meaningfully, especially for teams with compliance requirements, long retention needs, or pressure to reduce mean time to resolution.
Pricing Behavior at Scale: Graylog vs Grafana vs CubeAPM
Pricing differences between observability platforms tend to be modest at low volumes and significant at scale. Understanding how each model behaves as telemetry grows is essential for total cost of ownership projections.
Modeled Cost Overview
Disclaimer: These are directional estimates based on standardized telemetry assumptions, 30–90 day retention, and public pricing where available. Actual costs may vary by ingest volume, retention, metric cardinality, deployment model, contract terms, and discounts. Grafana and Graylog enterprise costs may require vendor quotes.
| Team Size | CubeAPM (est.) | Graylog Enterprise (est.) | Grafana Cloud (est.) |
| ~30 engineers | $1,950/month | $3,200/month | $4,800/month |
| ~125 engineers | $6,800/month | $11,400/month | $17,500/month |
| ~250 engineers | $14,400/month | $28,600/month | $38,200/month |
Key Pricing Dynamics to Watch
- Grafana Cloud: Usage is billed separately across signals. Public Grafana Cloud pricing lists logs at $0.40/GB ingested, log retention at $0.10/GB/month, and traces at $0.50/GB ingested. Metrics are billed by active series and scrape frequency, starting at $6.50 per 1,000 active series at a 60-second scrape interval. Grafana Cloud Pro includes 30 days of log and trace retention and 13 months of metric retention. Enterprise starts at $25,000/year. At scale, these separate meters can compound when log volume, trace volume, or metric cardinality grows.
- Graylog: Graylog Enterprise starts at $15,000/year and Graylog Security starts at $18,000/year, based on daily volume or annual consumption. Its consumption model focuses on Active Data written to the indexing tier, which can help teams separate high-value searchable logs from lower-priority archived data. Self-hosted deployments may still add infrastructure costs for Graylog, OpenSearch, MongoDB, and storage.
- CubeAPM: Flat per-GB pricing at $0.15/GB with no per-user, per-host, or per-module charges. All platform capabilities including APM, RUM, Synthetics, Infrastructure, Logs, and Traces are included in the same price. Context-aware smart sampling reduces effective trace ingestion volume by up to 80 percent, which directly lowers the monthly bill.
Data Retention

CubeAPM retention is a core architectural advantage. The Enterprise plan provides unlimited retention, while the self-hosted or BYOC deployment model means retention stops being a recurring SaaS upsell and becomes primarily a storage-capacity decision inside the infrastructure the customer already controls. For teams that need to revisit incidents months later, maintain compliance audit windows, or avoid paying more every time retention requirements grow, this model materially improves cost predictability.
Graylog uses configurable retention rather than a single fixed platform-wide limit. New index sets default to a time-size-optimizing window of approximately 30 to 40 days, but teams can extend retention through archive and tiered storage strategies depending on deployment and plan. That makes Graylog more flexible than a fixed SaaS retention model, though longer lookback still depends on how the environment is configured and managed and adds storage overhead in self-hosted deployments.
Grafana Cloud gives paying customers 30 days of retention for logs and traces, while metrics get 13 months on Pro. Log retention can be extended in 30-day increments at added cost, with public pricing listing log retention at $0.10/GB/month. Grafana Cloud Logs Export also lets teams export logs to their own object storage for long-term retention, compliance, or data-control needs.
Best-Fit Scenarios and Trade-offs
CubeAPM
Best for: Engineering teams running Kubernetes-based microservices who need full OpenTelemetry-native observability with stronger data control, predictable ingestion-based pricing, and deployment inside their own cloud or on-premises environment. It is especially relevant for teams that want unified MELT visibility without moving telemetry into an external SaaS platform.
Strengths: Full MELT coverage including logs, metrics, traces, and infrastructure visibility; OpenTelemetry-native ingestion; context-aware smart sampling for lower-noise debugging; data remains in the customer environment; vendor-managed operations model; SOC 2 and ISO 27001 certified; setup in under 60 minutes; no per-user fees.
Limitations: Not suited for teams that require purely off-prem SaaS without any infrastructure involvement. Strictly an observability platform and does not support SIEM or cloud security management workflows.
Graylog
Best for: Teams that need powerful, centralized log management with strong SIEM capabilities and the flexibility to self-host or deploy on-premises. Well-suited for IT operations teams, security analysts, and DevOps engineers whose primary operational signal is logs, including syslog, Windows events, application logs, and network device logs, alongside structured alerting and security investigation workflows.
Strengths: Strong full-text log search across OpenSearch/Elasticsearch; SIEM capabilities through Graylog Security edition; flexible pipeline-based log enrichment and routing; active-data-oriented consumption pricing model; flexible deployment across on-prem, hybrid, or cloud environments; open-source edition available.
Limitations: Not a native distributed tracing or APM platform. Teams that need trace-level debugging will need a separate APM or tracing backend. Self-hosted deployments also add operational overhead because Graylog commonly relies on components such as OpenSearch and MongoDB.
Grafana
Best for: Teams that need maximum flexibility in data visualization and observability across many data sources, and have the SRE capacity to assemble and operate the LGTM stack. Well-suited for organizations already running Prometheus or other open-source tooling who want to unify dashboards and add log and trace correlation without switching to a fully managed platform.
Strengths: Unmatched visualization depth with 300+ data source plugins; full MELT coverage when LGTM stack is assembled; strong Kubernetes-native monitoring; Adaptive Telemetry suite for cost control across metrics, logs, traces, and profiles; broad open-source community; FedRAMP-authorized Federal Cloud option (GA Oct 2025).
Limitations: Self-hosted LGTM deployments require setup and operational effort. PromQL and LogQL can have a learning curve. Grafana Cloud usage-based billing can grow with logs, traces, metrics, and retention. Core Grafana open-source projects use AGPLv3, which some enterprises may need to review with legal teams.
Decision Framework
Teams evaluating these three platforms typically prioritize one of the following needs. The table below maps common requirements to the most likely architectural fit, along with the key trade-off to evaluate.
| Primary Priority | Likely Best Fit | Key Trade-off to Consider |
| Centralized log management and SIEM | Graylog | No native distributed tracing; may need a companion APM tool |
| Full-stack observability with data ownership | CubeAPM | Not built for SaaS-only teams; no built-in SIEM |
| Flexible dashboards across many data sources | Grafana | LGTM setup and PromQL/LogQL learning curve |
| OpenTelemetry-native observability | CubeAPM | Runs in customer-controlled infrastructure, with vendor-managed ops |
| Kubernetes monitoring with rich dashboards | Grafana | Stack assembly and usage-based cloud billing |
| Predictable billing with no user fees | CubeAPM | Observability only; no cloud security module |
| SIEM and security analytics | Graylog Security | Logs-first platform; no native APM or tracing |
| Compliance-ready on-prem or VPC deployment | CubeAPM or Graylog | CubeAPM is observability-first; Graylog is log/SIEM-first |
Conclusion
CubeAPM, Graylog, and Grafana fit different observability needs.
CubeAPM is best for teams that want OpenTelemetry-native full-stack observability, stronger data control, and predictable ingestion-based pricing inside their own environment. Its main trade-off is that it is not a SIEM platform.
Graylog is best for centralized log management and SIEM workflows. Its main trade-off is limited native APM and distributed tracing, so teams may need a companion observability tool.
Grafana is best for flexible dashboards and composable observability across logs, metrics, and traces. Its main trade-off is the setup and operational effort of the LGTM stack, plus usage-based billing complexity in Grafana Cloud.
The right choice depends on whether your priority is log/security workflows, full-stack observability, data control, or pricing predictability.
Disclaimer: The information in this article reflects the latest details available at the time of publication and may change as technologies and products evolve.
FAQs
1. Is Graylog a full observability platform or mainly a log management tool?
Graylog is mainly a log management and SIEM platform. It is strong for log ingestion, search, alerting, and security workflows, but it is not a native tracing-first APM platform like CubeAPM or a fully assembled Grafana LGTM stack.
2. What makes CubeAPM different from Graylog and Grafana?
CubeAPM combines OpenTelemetry-native observability, customer-controlled deployment, and flat ingestion-based pricing at $0.15/GB. Compared with Graylog, it adds full-stack observability and tracing. Compared with Grafana, it offers a more pre-integrated platform instead of requiring teams to assemble LGTM components.
3. How does OpenTelemetry support compare across these platforms?
CubeAPM is positioned as OpenTelemetry-native. Grafana has strong OpenTelemetry support across the LGTM stack. Graylog supports OpenTelemetry log ingest through OTLP over gRPC, but its core design remains log-centric rather than full MELT observability.
4. Which platform handles data retention better for compliance use cases?
CubeAPM and self-hosted Graylog are stronger fits for customer-controlled long-term retention. Grafana Cloud gives 30 days for logs and traces on Pro, with paid retention extensions and Logs Export for customer-owned storage.
5. What is the best platform for Kubernetes-based microservices observability?
CubeAPM and Grafana are stronger fits for Kubernetes microservices observability. Grafana offers deep dashboarding and LGTM flexibility. CubeAPM offers a more integrated full-stack experience with APM, logs, infrastructure, and traces. Graylog is useful for Kubernetes logs, but not native tracing-first observability.
Teams usually migrate by sending telemetry through the OpenTelemetry Collector, then moving logs, traces, and metrics step by step. CubeAPM also positions itself as supporting incremental migration from existing agents and Prometheus-based setups, but migration time depends on the current stack, data volume, and instrumentation.







